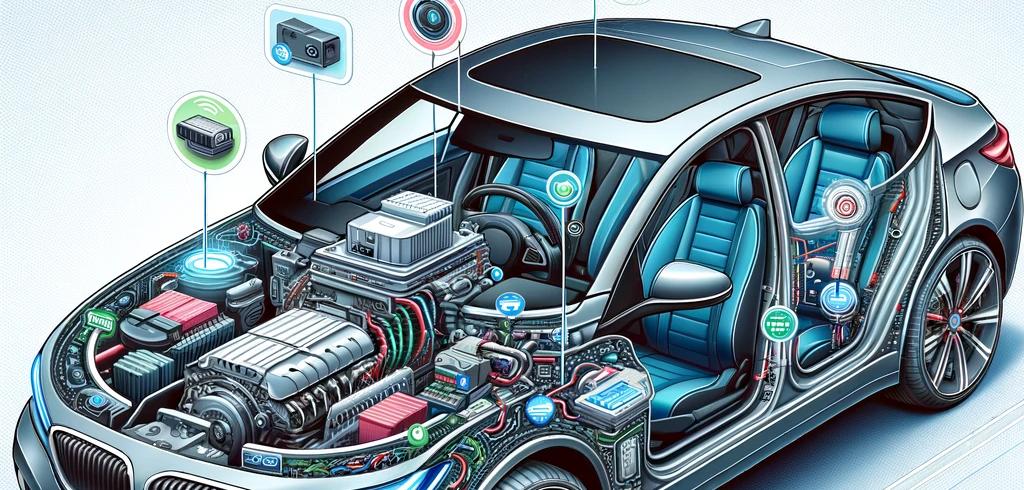
Next-Gen Auto Cyberdefenses: Navigating the Digital Highways of Connected Car Security
Introduction In the age of connected and autonomous vehicles, cybersecurity has emerged as a critical concern. Modern cars,...

Detailed Analysis of Profinet Packet in the Automation Network
Upon analyzing the network’s data traffic for Profinet communication, I discovered various types of packets. In order to...

Why EDR is Essential for Industrial Control Systems ? Let’s see!
How does EDR works? Endpoint detection and response (EDR) works by continuously monitoring and analyzing endpoint activity to...

NIST 800-82: Essential Guidelines for Industrial Control System Security
NIST 800-82 -Industrial Control System Guidelines NIST 800-82 is a publication from the National Institute of Standards and...

How to Better Train Your Automation Engineers on ISA/IEC 62443
The Colonial Pipeline attack exposed an ongoing problem facing the nation’s critical infrastructure: A gap in the cybersecurity workforce. Future...
Common cyber attack tactics used by adversaries for ICS
Tactics represent the “why” of an ATT&CK technique or sub-technique. It is the adversary’s tactical goal: the reason...

Major Cyber attack methods on an ethernet network switch
Some possible attack methods for ethernet switches are explained in this topic. These are quite common type of...

Securing Energy Infrastructure from Cyber Threats
Introduction Energy infrastructure is quite a large sector on Earth. It has evolved from the past 200 years...
Phases of ICS Cyber security Lifecycle from IEC 62443
Industrial Control System Cybersecurity Lifecycle The stages that a physical process or a management system goes through as...

Method of High Level Risk Analysis from IEC 62443.
The implementation of IEC 62443 begins with a risk analysis. High level risk analysis is a step wise...